13 January 2015 - New Year, same old scams ...
Sadly, the new year has not brought a change to the same scams that we received last year.
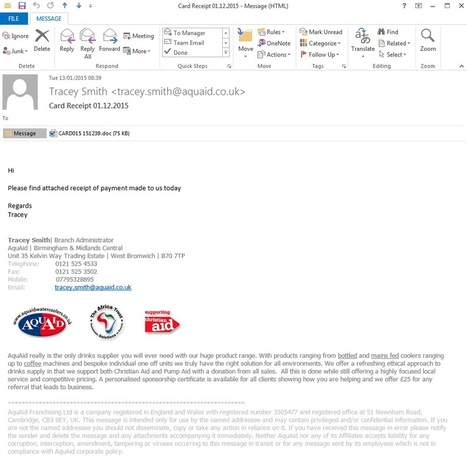
One scam email brought to our attention today resulted from a hack made on AquAid's email account. In response, AquAid has placed a recorded message on the telephone of Tracey Smith telling callers that the email is a scam, the attachment should not be opened and the email deleted.
Clearly this is becoming a more common problem for email users. So how can you tell whether the attachment is malware-infected? Most good email systems will detect malware-infected attachments and either delete or quarantine the email. Most good anti-virus systems will also jump into action as soon as you try to open a malware-infected file, but this relies on the technology being one step ahead of the malware - being aware of the signature of malware and able to detect it before you receive the email or open the attachment.
Our main precaution is that you should never open an email attachment from someone you're not expecting to receive an email from.
But what if you're not sure?
There are on-line file scanners available, to which you can upload a suspicious file. They will scan the file using one or more anti-virus engines, and let you know whether the file is OK to open or not. We thought we'd try a few to see whether they would spot the virus in the file attached to this email. The results were ... interesting.
Metascan Online - scanned the file with 40 malware scanners, but none of them reported any malware in the file. This list of malware scanners included Kaspersky (although the virus definitions being used were 1 day old)
Gary's Hood online virus scanner - scanned the file with 4 malware scanner, but none of them reported any malware in the file.
Fortiguard Center - scanned the file and confirmed that it was clean.
VirusTotal - scanned the file with 55 well known virus scanners. Only 2 (4%) of the 55 scanners (Avast and Kaspersky) spotted the file had a trojan horse (a form of malware) in it.
NoDistribute.com - scanned the file with 34 malware scanners. Only 3 (9%) of the 34 scanners Avast, Dr.Web and Kaspersky) spotted the malware.
Jotti's Malware scan - scanned the file with 22 malware scanners. Only 3 (14%) of the 22 scanners (Avast, G Data and Kaspersky) spotted the malware.
Assuming that these websites all submit to the genuine virus scanners (and there should be no reason to suspect they don't) then it casts some doubt over the reliability of the current anti-virus scanners to spot this simple malware. This reinforces our opinion that you should never open an email attachment from someone you're not expecting to receive an email from.
If you are concerned about anything in this notice, please contact us and we will be glad to discus our findings with you.
One scam email brought to our attention today resulted from a hack made on AquAid's email account. In response, AquAid has placed a recorded message on the telephone of Tracey Smith telling callers that the email is a scam, the attachment should not be opened and the email deleted.
Clearly this is becoming a more common problem for email users. So how can you tell whether the attachment is malware-infected? Most good email systems will detect malware-infected attachments and either delete or quarantine the email. Most good anti-virus systems will also jump into action as soon as you try to open a malware-infected file, but this relies on the technology being one step ahead of the malware - being aware of the signature of malware and able to detect it before you receive the email or open the attachment.
Our main precaution is that you should never open an email attachment from someone you're not expecting to receive an email from.
But what if you're not sure?
There are on-line file scanners available, to which you can upload a suspicious file. They will scan the file using one or more anti-virus engines, and let you know whether the file is OK to open or not. We thought we'd try a few to see whether they would spot the virus in the file attached to this email. The results were ... interesting.
Metascan Online - scanned the file with 40 malware scanners, but none of them reported any malware in the file. This list of malware scanners included Kaspersky (although the virus definitions being used were 1 day old)
Gary's Hood online virus scanner - scanned the file with 4 malware scanner, but none of them reported any malware in the file.
Fortiguard Center - scanned the file and confirmed that it was clean.
VirusTotal - scanned the file with 55 well known virus scanners. Only 2 (4%) of the 55 scanners (Avast and Kaspersky) spotted the file had a trojan horse (a form of malware) in it.
NoDistribute.com - scanned the file with 34 malware scanners. Only 3 (9%) of the 34 scanners Avast, Dr.Web and Kaspersky) spotted the malware.
Jotti's Malware scan - scanned the file with 22 malware scanners. Only 3 (14%) of the 22 scanners (Avast, G Data and Kaspersky) spotted the malware.
Assuming that these websites all submit to the genuine virus scanners (and there should be no reason to suspect they don't) then it casts some doubt over the reliability of the current anti-virus scanners to spot this simple malware. This reinforces our opinion that you should never open an email attachment from someone you're not expecting to receive an email from.
If you are concerned about anything in this notice, please contact us and we will be glad to discus our findings with you.
29 December 2014 - Post-Christmas IT security headache for the New Year

Merry Christmas from Liquid Speak!
We hope that all our readers had a very enjoyable Christmas, and the joy of receiving the latest Sony PlayStation or Microsoft XBox was not overshadowed by the IT security issues that faced Sony and Microsoft.
If your employees were lucky enough to receive shiny new smartphones for Christmas, then you should expect them to return to the office proudly sporting the new device muttering phrases such as, "Look, I can even get my work emails on here....." This exuberance after Christmas can easily turn into a New Year nightmare if not handled correctly, as each new smartphone connected to the company IT systems is another point of entry that need to be secured. Many companies fail to recognise these, so we thought we'd take this opportunity to remind you of the biggest risks.
1. Not locking the device - This is the first line of defence against unauthorised access to company data. Whether you lock your phone with a simple PIN or password, or use the iPhone 5S's fingerprint scanner, locking your device can make the difference between keeping a lost or stolen phone protected for long enough to either track it down or wipe it remotely.
2. Not having the most up to date versions of your apps - Apps are often released with vulnerabilities, and some security flaws manage to persist throughout multiple updates and iterations of the software. By the time developers finally get to patching the vulnerabilities in their apps users could be multiple versions behind if they aren't diligent about keeping them updated. Keeping your software up to date by downloading updates as soon as possible after they are released can prevent users from posing a security risk to their companies simply by using their apps.
3. Storing sensitive, work-related data on an unauthorised device - Storing your company's sensitive data on your private device isn't a problem if your company has a "Bring Your Own Device" (BYOD) policy to cover this. If it does, that means the company can monitor any private information being stored on your mobile device. It your company doesn't have a BYOD policy in place, then that's a bigger problem (see below) - storing company information on unauthorised devices and/or private devices when a BYOD policy isn't in place is just asking for a security breach. Even worse is if the employee is keeping the data in a location on the phone that is being synced up with cloud storage during backups. Keeping business and personal data separate is key.
4. Opening questionable content - There are a number of ways users can access shady content via their mobile device. SMS text message pose a particular threat - spam texts containing links to sites that pose threats are not unheard of, for example, and users should avoid opening links from sources they don't recognise.
5. Downloading apps from untrusted sources - Apps that are released through Apple's App Store or Google Play Store will have been through some form of checking. However, if you bypass these locations and download apps from other third-party app stores, there is no telling what kind of malicious software you may end up with. It may not be apparent at first, but could prove disastrous in the long run.
6. Not having a, or adhering to your company's, social media policies - Most companies have some kind of policy in place regarding disclosing sensitive information or data over social channels, so it's important that you learn it so that you can use social media on your mobile device responsibly. Some policies will say you cannot disclose any information on social media. While a social media slip-ups may be obvious, like disclosing insider information or data, even sharing seemingly innocuous information about your company can be problematic and leave you or your company with a very serious problem.
7. Not equipping devices with some form of Mobile Device Management solution or encryption - Smart companies ensure they use a Mobile Device Management (MDM) solution to control what data their employees can access and how they can interface their smartphones to company systems. Companies that don't have such a system to control access are asking for trouble. This is especially true where companies allow employees to "bring your own device" (BYOD) to the workplace, in which case there is no telling what is being connected to the company IT systems unless a good MDM solution is in place.
8. Using public or unsecured Wi-Fi - Wi-Fi is faster and cheaper than mobile data, but if something looks too good to be true, maybe it is? Only connect to secure Wi-Fi connections that use encryption. Open or unprotected networks are very risky, especially for users that are carrying sensitive company data on their devices. Apart from making it easy for others to access your mobile device's information by sharing the same network, public Wi-Fi can even allow attackers to hijack your device through your apps. A vulnerability was recently discovered in some iOS apps that allowed attackers to intercept the traffic between the app and a public Wi-Fi server and instead send their own data to the victim's phone.
9. Not disposing of mobile devices securely - So your employees have shiny new phones? What did you or they do with the old ones? Handed them over to family members, or friends, or eBay? What about the data that was on there? Is it securely wiped? The best way to be sure is to shred the device, but that renders it useless. If the data was encrypted on the device and that encryption key is removed, that is a far better solution. Mobile Device Management or device encryption is a must if you're going to keep company information on a mobile device.
If you are concerned that your staff might not be adhering to all of the above, then please contact us and we will be glad to work with you to ensure that your employees use smartphones responsibly and safely.
We hope that all our readers had a very enjoyable Christmas, and the joy of receiving the latest Sony PlayStation or Microsoft XBox was not overshadowed by the IT security issues that faced Sony and Microsoft.
If your employees were lucky enough to receive shiny new smartphones for Christmas, then you should expect them to return to the office proudly sporting the new device muttering phrases such as, "Look, I can even get my work emails on here....." This exuberance after Christmas can easily turn into a New Year nightmare if not handled correctly, as each new smartphone connected to the company IT systems is another point of entry that need to be secured. Many companies fail to recognise these, so we thought we'd take this opportunity to remind you of the biggest risks.
1. Not locking the device - This is the first line of defence against unauthorised access to company data. Whether you lock your phone with a simple PIN or password, or use the iPhone 5S's fingerprint scanner, locking your device can make the difference between keeping a lost or stolen phone protected for long enough to either track it down or wipe it remotely.
2. Not having the most up to date versions of your apps - Apps are often released with vulnerabilities, and some security flaws manage to persist throughout multiple updates and iterations of the software. By the time developers finally get to patching the vulnerabilities in their apps users could be multiple versions behind if they aren't diligent about keeping them updated. Keeping your software up to date by downloading updates as soon as possible after they are released can prevent users from posing a security risk to their companies simply by using their apps.
3. Storing sensitive, work-related data on an unauthorised device - Storing your company's sensitive data on your private device isn't a problem if your company has a "Bring Your Own Device" (BYOD) policy to cover this. If it does, that means the company can monitor any private information being stored on your mobile device. It your company doesn't have a BYOD policy in place, then that's a bigger problem (see below) - storing company information on unauthorised devices and/or private devices when a BYOD policy isn't in place is just asking for a security breach. Even worse is if the employee is keeping the data in a location on the phone that is being synced up with cloud storage during backups. Keeping business and personal data separate is key.
4. Opening questionable content - There are a number of ways users can access shady content via their mobile device. SMS text message pose a particular threat - spam texts containing links to sites that pose threats are not unheard of, for example, and users should avoid opening links from sources they don't recognise.
5. Downloading apps from untrusted sources - Apps that are released through Apple's App Store or Google Play Store will have been through some form of checking. However, if you bypass these locations and download apps from other third-party app stores, there is no telling what kind of malicious software you may end up with. It may not be apparent at first, but could prove disastrous in the long run.
6. Not having a, or adhering to your company's, social media policies - Most companies have some kind of policy in place regarding disclosing sensitive information or data over social channels, so it's important that you learn it so that you can use social media on your mobile device responsibly. Some policies will say you cannot disclose any information on social media. While a social media slip-ups may be obvious, like disclosing insider information or data, even sharing seemingly innocuous information about your company can be problematic and leave you or your company with a very serious problem.
7. Not equipping devices with some form of Mobile Device Management solution or encryption - Smart companies ensure they use a Mobile Device Management (MDM) solution to control what data their employees can access and how they can interface their smartphones to company systems. Companies that don't have such a system to control access are asking for trouble. This is especially true where companies allow employees to "bring your own device" (BYOD) to the workplace, in which case there is no telling what is being connected to the company IT systems unless a good MDM solution is in place.
8. Using public or unsecured Wi-Fi - Wi-Fi is faster and cheaper than mobile data, but if something looks too good to be true, maybe it is? Only connect to secure Wi-Fi connections that use encryption. Open or unprotected networks are very risky, especially for users that are carrying sensitive company data on their devices. Apart from making it easy for others to access your mobile device's information by sharing the same network, public Wi-Fi can even allow attackers to hijack your device through your apps. A vulnerability was recently discovered in some iOS apps that allowed attackers to intercept the traffic between the app and a public Wi-Fi server and instead send their own data to the victim's phone.
9. Not disposing of mobile devices securely - So your employees have shiny new phones? What did you or they do with the old ones? Handed them over to family members, or friends, or eBay? What about the data that was on there? Is it securely wiped? The best way to be sure is to shred the device, but that renders it useless. If the data was encrypted on the device and that encryption key is removed, that is a far better solution. Mobile Device Management or device encryption is a must if you're going to keep company information on a mobile device.
If you are concerned that your staff might not be adhering to all of the above, then please contact us and we will be glad to work with you to ensure that your employees use smartphones responsibly and safely.
1 December 2014 - Are your employees winding down for Christmas?
As we head into the final few weeks before Christmas, the festive season is well upon us. Christmas is being well advertised everywhere you look and your staff are probably looking forward to spending an exciting time with their family and friends. Its probably also likely that you'll be receiving lots of unexpected Christmas cards from suppliers you'd forgotten about.
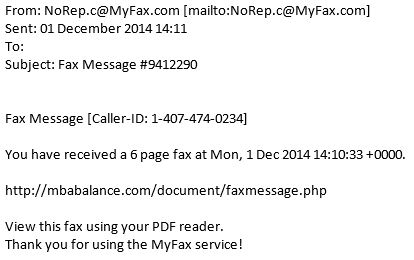
Into the Liquid Speak offices, we were somewhat surprised to receive an unexpected email telling us there was a fax waiting to be downloaded. Fortunately, our finance manager was not too engrossed in Christmas shopping to merely click on the link, for the first rule of emails applies even more so when your guard is down! Never open an attachment or click on a link in an email you weren't expecting.
Had our finance manager clicked on the link, we're not sure what sort of festive gift would have been delivered, but it's highly likely that this would be something like a virus or similar.
If you are concerned that your staff might have been less than focused on their work and may have clicked on one of these emails, then please contact us and we will be glad to resolve any problems that have been created.
Into the Liquid Speak offices, we were somewhat surprised to receive an unexpected email telling us there was a fax waiting to be downloaded. Fortunately, our finance manager was not too engrossed in Christmas shopping to merely click on the link, for the first rule of emails applies even more so when your guard is down! Never open an attachment or click on a link in an email you weren't expecting.
Had our finance manager clicked on the link, we're not sure what sort of festive gift would have been delivered, but it's highly likely that this would be something like a virus or similar.
If you are concerned that your staff might have been less than focused on their work and may have clicked on one of these emails, then please contact us and we will be glad to resolve any problems that have been created.
11 November 2014 - Patch Tuesday comes around again
|
The second Tuesday of every month is an important day in the world of IT security for two reasons. Firstly, it is the day on which the major software manufacturers (Microsoft, Adobe, etc.) release patches for their operating systems and applications. These patches fix security problems that the manufacturers have identified in their operating systems and applications. However, more importantly, it is the day that the software manufacturers announce to the world the existence of the security problems that they are releasing patches for!
Therefore, if you do not implement the patches that have been released, then you will remain exposed to having the weaknesses in your IT security ... and these weakness are now public knowledge. Whilst Windows PCs may automatically update themselves with the patches (if automatic updates are turned on), servers may need to be patched manually and restarted, so it is worth checking with your IT support provider whether this is being done. One final thought - Microsoft stopped patching the Microsoft Windows XP operating system on 8 April 2014, but a number of the security problems that have subsequently been identified and patched in Windows 7 are also known and un-patched security problems in Windows XP, so if your company is still running Windows XP on its PCs then you run a higher risk of suffering an IT security breach. If you are concerned that your company might be vulnerable to security flaws due to a lack of patching or because you're still using Windows XP on PCs connected to the internet, then please contact us and we will be glad to review your systems and help you protect against these risks. |
8 October 2014 - Google unwittingly indexes confidential information

Google is a very powerful search engine. It uses search 'spiders' that crawl over the internet to index the information on web servers, and then presents this to internet users who are looking for information. If a web server is publicly-accessible, then Google will index the information on it when it finds it.
Unfortunately, this is what happened when MBIA, Inc., the United States' largest bond insurer, incorrectly configured an Oracle Reports database server. The reporting server was only intended to be accessible to internal staff at the company, but was accidentally exposed to the internet. The Google search engine, along with several other search engines, automatically indexed the information that was being presented to the internet, allowing anyone to accessible the private data. The most serious information exposed included detailed instructions on how to authorise new bank accounts for deposits, including the forms and fax numbers needed to submit the account information.
If your company uses Oracle Reports Services, please ensure that your IT team have read and implemented Oracle’s advice on securing these systems.
If you are concerned that your company information might be accessible to the internet, please contact us and we will be glad to review your systems.
Unfortunately, this is what happened when MBIA, Inc., the United States' largest bond insurer, incorrectly configured an Oracle Reports database server. The reporting server was only intended to be accessible to internal staff at the company, but was accidentally exposed to the internet. The Google search engine, along with several other search engines, automatically indexed the information that was being presented to the internet, allowing anyone to accessible the private data. The most serious information exposed included detailed instructions on how to authorise new bank accounts for deposits, including the forms and fax numbers needed to submit the account information.
If your company uses Oracle Reports Services, please ensure that your IT team have read and implemented Oracle’s advice on securing these systems.
If you are concerned that your company information might be accessible to the internet, please contact us and we will be glad to review your systems.
19 August 2014 - 4.5 million patient records exposed as a result of hack in the US

It was reported today that US hospital group, Community Health Systems, was the victim of hackers who were able to gain access to 4.5 million patient records during a cyber attack earlier this year. During the attack, the hackers (reported to be from China) were able to bypass the company's security systems to access the personal data of patients, including names, social security numbers and addresses. The company is reporting that no actual data was accessed, but they are writing to all the potentially affected patients to offer free identity-theft protection services.
If you store personal data relating to customers or employees, your company is legally bound by the Data Protection Act to ensure that "Appropriate technical and organisational measures shall be taken against unauthorised or unlawful processing of personal data and against accidental loss or destruction of, or damage to, personal data" which means that you need to design and organise your security to fit the nature of the personal data you hold and the harm that may result from a security breach; make sure you have the right physical and technical security, backed up by robust policies and procedures and reliable, well-trained staff; and be ready to respond to any breach of security swiftly and effectively.
If you are concerned that your data might be at risk, please contact us and we will be glad to review your security measures and make recommendations.
If you store personal data relating to customers or employees, your company is legally bound by the Data Protection Act to ensure that "Appropriate technical and organisational measures shall be taken against unauthorised or unlawful processing of personal data and against accidental loss or destruction of, or damage to, personal data" which means that you need to design and organise your security to fit the nature of the personal data you hold and the harm that may result from a security breach; make sure you have the right physical and technical security, backed up by robust policies and procedures and reliable, well-trained staff; and be ready to respond to any breach of security swiftly and effectively.
If you are concerned that your data might be at risk, please contact us and we will be glad to review your security measures and make recommendations.
8 August 2014 - USB Devices may be a security risk

It is being reported that USB devices may contain a security bug that allows them to perform unintended actions on your computer. This is because, when you plug in a USB device, your computer asks it what it is. Researchers found that USB memory sticks could be infected with code that that would make the computer believe that the USB memory stick was a keyboard and would then accept commands as if they had been typed, such as instructing the computer to connect to a malicious website and download a virus.
As with all things related to computers, you should be cautious about accepting, on face value, something you are told, especially if it has come from someone you don't know. So, if someone unexpectedly sends you a USB memory stick that you weren't expecting, don't just plug it into your PC without considering the potential risks.
If you would like further advice about this or other IT risks that could face your company, please contact us, and we will be glad to talk to you.
As with all things related to computers, you should be cautious about accepting, on face value, something you are told, especially if it has come from someone you don't know. So, if someone unexpectedly sends you a USB memory stick that you weren't expecting, don't just plug it into your PC without considering the potential risks.
If you would like further advice about this or other IT risks that could face your company, please contact us, and we will be glad to talk to you.
6 August 2014 - New site recovers files locked by Cryptolocker

Since September 2013, a very dangerous piece of Malware called 'Cryptolocker' has been infecting PCs around the world. PCs are infected when a user opens a file attached to an email such as those from a shipping company saying they have a package for you, or from the tax authorities to say they have a tax refund for you. Similar scam emails have been circulating for many years, but Cryptolocker represented a step forward in the lengths which criminals would go to benefit from their crimes. Instead of annoying popups, Cryptolocker scrambles all the files on an infected PC and then prompts the user to pay around £250 to have the files unscrambled. The only other choice was to delete the files. As a result, it is estimated that criminals made $27million in just over 2 months from Cryptolocker ransom payments.
Due the the way in which the data files are encrypted, the security has been impossible to crack, until now. It was reported today that two security firms have launched a website that helps victims to potentially recover their files. The website, www.decryptcryptolocker.com, can provide a recovery program for victims. All that is required is for victims to enter their email address and upload one of the encrypted files from their computer, and the service will email a link that victims can use to download a recovery program to decrypt all of their scrambled files.
Even though victims of previous versions of Cryptolocker can now potentially recover their files by using this website, it won't be long before new strains of Cryptolocker start circulating the internet, and it usually takes a few days before anti-virus software is updated to spot these files. The only true protection against these sort of viruses is vigilance on the part of the users. You should trust no one, and expect the unexpected. As soon as you receive an email that you are not expecting (even if it appears to be from someone that you know) with a file attachment, or a link to a website, you should be suspicious!
If your company has been infected by the CryptoLocker malware, this may help you to recover files that you may have thought were previously lost. If you would like assistance with this, please contact us, and we will be happy to help your company if we can.
Due the the way in which the data files are encrypted, the security has been impossible to crack, until now. It was reported today that two security firms have launched a website that helps victims to potentially recover their files. The website, www.decryptcryptolocker.com, can provide a recovery program for victims. All that is required is for victims to enter their email address and upload one of the encrypted files from their computer, and the service will email a link that victims can use to download a recovery program to decrypt all of their scrambled files.
Even though victims of previous versions of Cryptolocker can now potentially recover their files by using this website, it won't be long before new strains of Cryptolocker start circulating the internet, and it usually takes a few days before anti-virus software is updated to spot these files. The only true protection against these sort of viruses is vigilance on the part of the users. You should trust no one, and expect the unexpected. As soon as you receive an email that you are not expecting (even if it appears to be from someone that you know) with a file attachment, or a link to a website, you should be suspicious!
If your company has been infected by the CryptoLocker malware, this may help you to recover files that you may have thought were previously lost. If you would like assistance with this, please contact us, and we will be happy to help your company if we can.


